 Today is valentines day, but, much more importantly, it is also I love Free Software Day. That’s the day we show appreciation to all the Free Software (Free as in Freedom, but also often Free as in beer) Developers out there, who are working, mostly in their spare time, mostly unpaid, to make the tools we use every day work. This blog post is an experiment. I will try to list all the free software I use every day, and I will probably fail, just because it is all around us.
Today is valentines day, but, much more importantly, it is also I love Free Software Day. That’s the day we show appreciation to all the Free Software (Free as in Freedom, but also often Free as in beer) Developers out there, who are working, mostly in their spare time, mostly unpaid, to make the tools we use every day work. This blog post is an experiment. I will try to list all the free software I use every day, and I will probably fail, just because it is all around us.
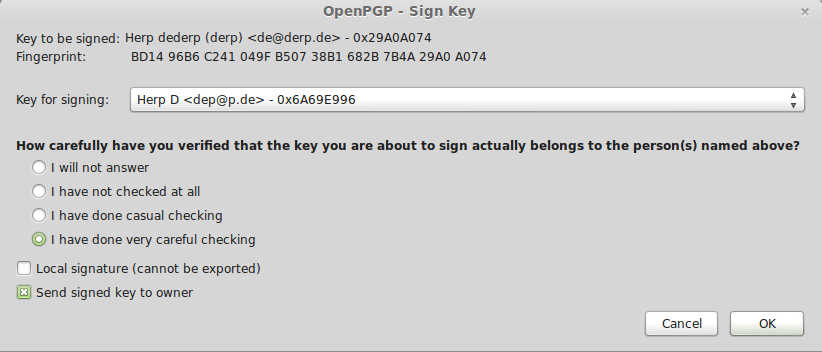
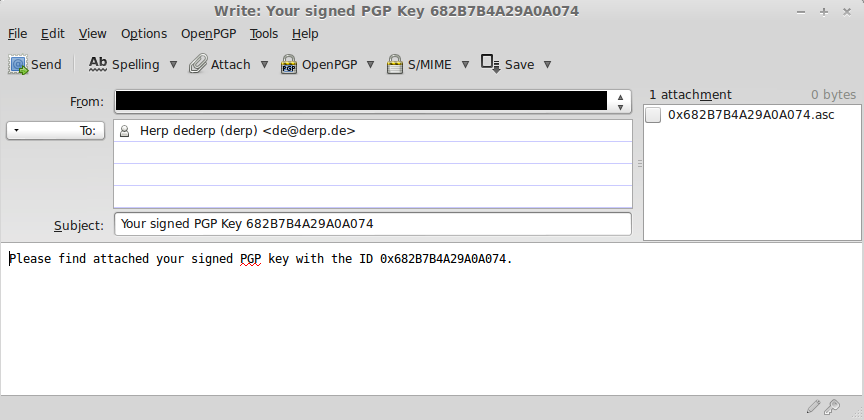
In the morning, when I start my Laptop, it boots into Linux Mint, which uses a plethora of Free libraries and programs like Grub, the Linux Kernel, and so on. After logging in, Tor, Pidgin with the OTR plugin, and the OwnCloud client automatically start up. I launch Thunderbird (which encrypts eMails using GnuPG) and Firefox (with a number of plugins) and go about my day.
When I need to do something on my server, I use OpenSSH or Mosh in a bash shell. The shell also runs Z (a handy little tool that makes navigating your computer much easier). On the server, I run the usual suspects (A server version of Ubuntu, Apache, MySQL, PHP, WordPress with some plugins, Mediawiki, OwnCloud, Piwik, OpenSSL, …) and some more specialized software like Ejabberd (a very nice jabber server), gitolite, and a Tor relay.
When I want to make short notes, I use gedit. For slightly longer texts, I have LibreOffice. And if I have to take notes or write texts in university, I use LaTeX with Texmaker and a bunch of extra packets. When editing images, I use Gimp or Inkscape, and for Audio, there’s Audacity. I watch videos using VLC and listen to music with Banshee. My passwords are securely stored using the KeePassX password manager, and the whole disk is encrypted with ecryptfs.
When I develop software, I use Git for versioning and, if possible, Python for my programming language (my code editor, Sublime Text, is one of the few pieces of non-free software I run on a regular basis). I also use a large number of command line utilities like grep, find, htop, wget, netcat, and so on.
On my android phone, I run CyanogenMod, a modified version of Android. I use TextSecure, CSipSimple, K9 Mail and APG for encrypted communication. Podcasts are retrieved using AntennaPod, I navigate using OsmAnd and Liberario, and use Twitter with Twidere. I own a couple of Raspberry Pi’s running Linux and an APU-Board running IPCop. In my window, I have a router running a Freifunk node with the Gluon Firmware.
Every single piece of software I just mentioned is Free Software (and I am sure I have forgotten some of the tools I use every day). Every single one of them is provided to me (and the rest of the world) free of charge. They are supported by communities of developers working on them in their spare time. In return, they expect nothing from us.
This is awesome.
These people do not get enough appreciation for their hard work, let alone donations. The developer of the single most important piece of technology for encrypted eMails, used by millions, almost went broke. This should be an indicator that something is wrong. Free Software is the only thing I know of where people seem to think that it is okay to use it, expect it to work and be updated, and not give anything in return.
It’s true that many developers work on Free Software because they believe in it, and because they like doing it, and that they don’t expect to be able to make a living from it. But you cannot expect people to give their full attention to these projects if they need to worry about getting food on the table. These people are donating their free time to these projects, and they deserve our thanks and support, instead of being sneered at because they would like to continue doing what they are doing and still be able to eat.
So, I love Free Software, and I try to do my part as best I can. There are too many great projects to donate to them all, but I regularily donate to some of them. If I encouter bugs, I report them. If I write my own software, I put it online under a Free Software license so others can benefit from it (as much as you can benefit from my terrible code at least). And I try to raise awareness.
Free software is awesome. Let’s help keep it awesome by keeping the developers motivated. Be it with a donation, a contribution of code, or even just a quick “thank you”. Give back to the community that gives you the things you use every day. To the developers of Free Software, whereever you may be: Thank you. Thank you for being awesome.
Note: Since it was published, this post was edited in the following way: I replaced Öffi with Liberario, as Öffi isn’t Free Software (thanks to @FSFE for pointing that out).